Government agencies should start implementing measures to prevent ransomware groups from accessing them, says the Department of Information and Communications Technology (DICT).
This statement came after the Philippine Health Insurance Corporation (PhilHealth) was hacked by the Medusa ransomware group last Friday, September 22. They demanded $300,000 (P17,063,850) in ransom money for the stolen data.
PhilHealth disabled access to all its systems, including the website, the member portal, the health care institution (HCI) portal and the e-claims platform.
In an update on September 23, PhilHealth assured its members that their personal and medical information were not compromised and leaked.
The state insurer shall continue its operations manually while working on restoring affected systems in the meantime.
Actions, steps to take
Ransomware is a type of malware wherein an attacker locks or encrypts data from a victim’s device to be ransomed for a considerable amount of money.
RELATED: Rundown: Ransomwares detected in the Philippines, other SEA countries
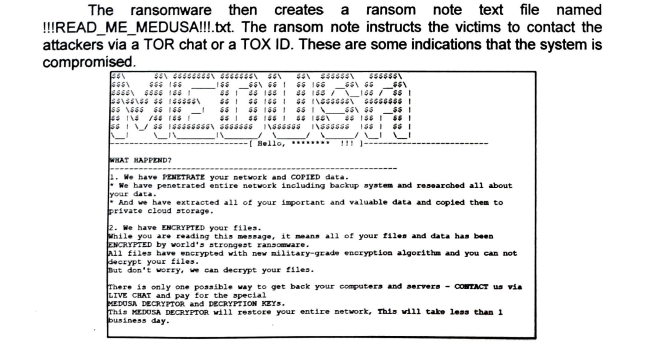
In an advisory, the DICT shared a sample ransom note that perpetrators behind the spread of ransomware create for their victims.
“The ransom note instructs the victims to contact the attackers via a TOR chat or a TOX ID,” the department said.
The DICT thus asked government agencies and the public to take action once their systems get compromised by Medusa ransomware.
Some of the recommendations in the advisory are:
- Backing up files, systems, processes, and other digital assets
- Prohibiting the use of illegal software and unlicensed programs, especially those downloaded from the internet, in all government offices
- Reviewing the access management policies of the organization, including the use of computers not issued by the government
- Implementing a recovery plan to properly store multiple copies of sensitive or proprietary data in different secure locations
Below are the rest of DICT’s recommended actions in case of any cybersecurity attack such as the Medusa ransomware incident.
DICT also recalled that the Medusa ransomware has been observed since June 2021.
The agency explained that individuals distribute Medusa ransomware by “exploiting publicly exposed Remote Desktop Protocol (RDP) servers either through brute force attacks, phishing campaigns or by exploiting existing vulnerabilities.”
From emails, websites, apps
In a video posted on September 25, the Philippine National Police-Anti-Cybercrime Group (PNP-ACG) said that employees may unintentionally give access to ransomware if they go to suspicious websites or click sketchy email attachments.
“Nakakapasok to kunwari na-click ng employees natin o na-click natin ang mga attachments sa email o mga infected websites na napasok or meron din vulnerabilities sa ating software,” PNP-ACG spokesperson PCPT. Michelle Sabino said.
Sabino shared the step-by-step infiltration process in a ransomware incident:
- Files and other types of data stored in an infected device get encrypted or locked.
- Owners or administrators thus lose access to their files.
- Scammers will give instructions to their victims on how their data can be unlocked.
- They will also ask for money as ransom for a decryption key to their files.
“So, ineencrypt tapos pag nagbayad na kayo, ibibigay nila yung decryption key,” Sabino said.
She advised the public to install anti-virus software and keep it up to date.
“Ito yung magdedetect, sila yung pag nakita o merong attempt, ibo-block na nila. Pag nakita na nila na parang ransomware to, bago pa ma-infect yung system niyo, nadedetect na nila,” she said.
The PNP-ACG spokesperson also emphasized the need to train employees on email security measures, domain name system (DNS) and web filtering services.
“Kailangan i-train ang employees to be cautious about opening emails. Usually, ang ransomware nanggagaling sa emails,” Sabino said.
“Gumamit tayo ng DNS and web filtering services na makakatulong sa pag block ng mga connections lalo na pag meron silang nakitang malicious websites,” she also suggested.
Moreover, Sabino also cautioned the public from downloading applications online.
“Para ma-prevent din na nagdodownload tayo ng mga app na mga pinapadala satin na di natin alam ransomware pala,” she said.