Some scammers have shifted from text messages to messaging apps in order to target victims following the SIM registration, according to a cybersecurity expert.
Nap Castillo, Manager of Systems Engineering of Fortinet Philippines, explained this during a briefing of the company’s latest study, “FortiGuard Labs 1H 2023 Global Threat Landscape Report,” at the New World Hotel in Makati City on September 21.
The report showed data on the number of detected cybersecurity threats, rising trends in online scams and other cybercrimes, and the behavior of organizations in dealing with cybersecurity threats.
Here, Castillo revealed that some scammers have adapted and shifted to using online messaging platforms following the implementation of the SIM registration law.
“The security hygiene of the telco environment is different from IT networks. It is actually easier to secure the IT network as compared to the mobile network,” Castillo said.
“That’s why even with this SIM card registration that we already have, the cybercriminals actually transfer to over-the-top applications like WhatsApp and Viber. Dun na tayo nakakareceive ng mga scams. Nawala na yung sa SMS (short messaging system),” he added.
“These are hosted outside of the Philippines that the government has no control over,” the Fortinet representative further said.
WhatsApp Messenger and Viber are both encrypted chat apps. The former is owned by a company in the United States and the latter is from Japan.
Castillo described text scams as a form of “weaponizing” SMS to target potential victims.
“If you notice on the text scams, most of them contain links. These links will link you to a weaponized file or a malicious website that can infect not only your mobile phone but also your other devices,” he said.
Multiple online scams spiked among Filipino users during the COVID-19 pandemic amid the gradual digitization in the country.
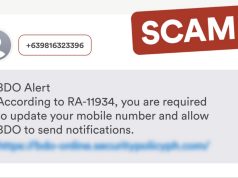
These include text scams where recipients receive suspicious job offers, fake delivery notifications, fake bank alerts and other unsolicited messages.
RELATED: ‘Dapat walang clickable link’: BSP urges banks, financial institutions amid scam reports | New text scam? Client asked of private info via SMS before supposed item delivery | Mobile wallet app starts hiding some letters in recipient names amid text scam surge | Inclusive scammer? TV host shares receiving text scam with name… and gender pronoun
Other methods of transmitting infected files
Castillo explained that scammers or cybercriminals start to look for vulnerable targets, whether it be on the internet or on different mobile devices.
He noted that they do this to secure a huge loot from a single attack.
“The cybercriminals do not send attacks blankly or blindly,” Castillo said.
After determining their targets, they will “weaponize” or load different file types with malware.
“When we say weaponization phase, this is where the cybercriminals prepare the workload. Wine-weaponize nila yung file, may it be excel file or word file,” he explained.
Castillo shared the next step—delivery of the “weapon” to victims.
He mentioned different delivery methods that scammers commonly perform, which include:
- Fake news flash in emails
- Delivery alerts where a recipient’s credit card supposedly gets charged
- Social media scams from lewd photos and videos
- Malicious URLs of websites
- USBs and USB ports
These steps are part of the seven-step process on how malware runs inside networks and devices called the Cyber Kill Chain.
After delivering the files with malware, the succeeding steps are:
- Exploitation
- Installation of the malware
- Establishment of a command and control
- Execution of actions to accomplish their goals
READ: Crypto heists seen to pose more danger in cybersecurity in 2023 —report